Verichains & Fireblocks Vulnerability Disclosures: No Impact to Capsule

We’re writing this brief post to address two recent reports of MPC-related vulnerabilities.
TSShock (Verichains)
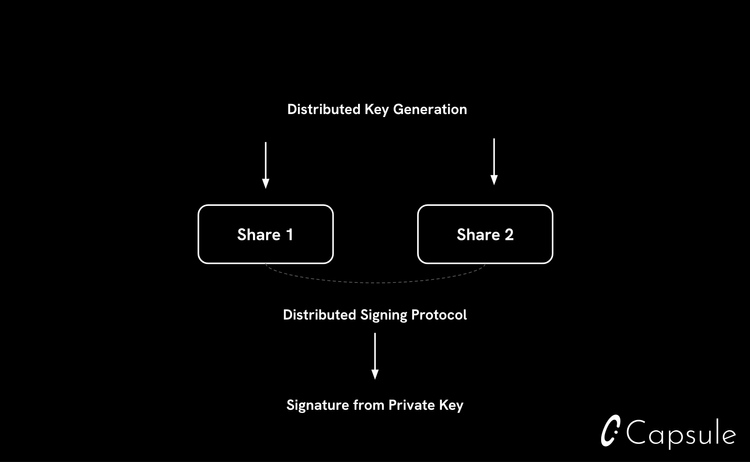
Verichains has found bugs in implementations of protocols based on the GG family, CGGMP- which is used by Capsule- being one of them. This family is particularly susceptible because of the use of a share conversion protocol, during which a few secret key elements are shared in a hidden form under an RSA modulus.
Exploiting this vulnerability requires a modified cheating participant implementation during signing. In Capsule’s case, the only participants are Capsule and the client. The only participant that would have anything to gain would be Capsule themselves (or hackers with access to Capsule’s servers)- and therefore assuming trust in Capsule’s servers running an unmodified version of this scheme, (including absence of them being compromised) there are no impacts to integrity of keys created with Capsule.
At this time, our systems have been upgraded to include a fix for this issue.
We note that keys previously generated would only be susceptible to the above vulnerability in the event Capsule’s systems were compromised by an attacker at the point of key generation. We do not have reason to believe this was the case, and note that the above detail would be true of any system using an impacted implementation.
BitForge (Fireblocks)
We additionally reviewed the recent Fireblocks-reported BitForge vulnerability disclosure and can confirm that there has been no impact to Capsule’s systems as a result of this disclosed vulnerability.
We thank all parties involved with disclosure and mitigation of both these issues.